Protecting Data from Ransomware and other Attacks
August 2021 by Ulf T. Mattsson
Attackers may already be in your environment and constantly find new ways to avoid detection. Make sure that your data is private and protected in transit, in use, in memory, and at rest. Sensitive data can be secured and protected by a robust data backup plan so systems can quickly be restored. A multi-layered defense can help to create a good security posture and how to discover unusual activity on your sensitive data.
The Threat Landscape
Attacks involving Phishing, Ransomware, Misconfiguration, Stolen credentials, and Mis-delivery continued to increase in 2020 according to Verizon DBIR and 10% of all breaches involved ransomware. The U.S. Secret Service noted that most organizations had adequate data backup, but cyber actors shifted their focus to the exfiltration of sensitive data and threatening to publicize the data unless additional ransom was paid.
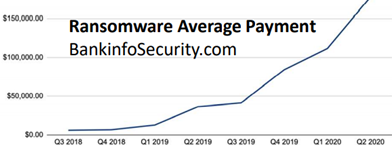
USA had 80% of the victims of ransomware in 2020 followed by Australia with 79% and Telecom had 76% of the victims followed by Education with 73% according to (ISC)2. This the trend in ransomware payments according to Bankinfo Security:
In early 2021 ransomware hit for example hit COLONIAL PIPELINE, QUANTA, NATIONAL BASKETBALL ASSOCIATION (NBA), BRENNTAG, ACER, JBS FOODS, AXA, and other victims according to Illinois.touro.edu. A ransom of between $7.5 million and $50 million US Dollars was demanded in several of these attacks and the hacker group disrupted gas supplies all along the East Coast of the United States, gained access to more than 3 TB of data including Apple product blueprints and other confidential data.
Prevent Attacks
According to “NIST IR 8374 CYBERSECURITY FRAMEWORK FOR RANSOMWARE”:
1. Maintain antivirus & patching
2. Allow only authorized apps
3. Limit personally owned devices
4. Limit administrative privileges
5. Limit personal apps
6. Avoid unknown files or links
7. Block ransomware sites
Recover after Attacks
According to “NIST IR 8374 CYBERSECURITY FRAMEWORK FOR RANSOMWARE” this can help recover from a future ransomware event:
1. Develop and implement an incident recovery plan with defined roles and strategies for decision making.
2. Carefully plan, implement, and test a data backup and restoration strategy—and secure and isolate backups of important data.
3. Maintain an up-to-date list of internal and external contacts.
Defend Users and Resources
A top-down approach to create strong ransomware mitigation can be built on NIST SP 800-207 Zero Trust Architecture (ZTA) that establishes the following Enterprise security characteristics:
1. Maintaining data protection at rest and in transit
2. Remediating device vulnerabilities that could result in unauthorized access to Data stored on or accessed by the device, and misuse of the device
3.Mitigating malware execution on the device that could result in unauthorized access to data stored on or accessed by the device, and misuse of the device
4. Mitigating the risk of data loss through accidental, deliberate, or malicious deletion or obfuscation of data stored on the device
5. Maintaining awareness of and responding to suspicious or malicious activities within and against the device to prevent or detect a compromise of the device
ZTA is based on understanding who the users are, which applications they are using and how they are connecting:
1. Enforce policy that ensures secure access to your data
2. Controls should be as close to the protect surface as possible, creating a micro perimeter around it
3. This micro-perimeter moves with the protect surface, wherever it goes
4. Continue to monitor in real time
ABAC (Attribute-based access control) can dynamically enforce policies based on a wide range of attributes (user attributes, resource attributes, object, environment attributes etc.) to protect data.
Data Security for Hybrid Cloud
Create data security policies and rules to protect data at rest and in transit. Use tokenization, anonymization, encryption, and other privacy models that are defined in the INTERNATIONAL DATA PRIVACY STANDARD ISO/IEC 20889.
Centrally manage enterprise users and continuously monitors security behavior across hybrid cloud.
Consistency across on-premises encryption and key management systems is often preferred to leverage the same tool and skills across multiple clouds. Issues with trust and cloud provider lock-in considerations are common concerns to enable easy migration to other cloud service providers.
Secure Applications and Data
80% of all attacks in 2020 involved servers and 53% target WEB servers according to Verizon DBIR.
OWASP “A3:2017 Sensitive Data Exposure” is highlighting that many web applications and APIs do not properly protect sensitive data, such as financial, healthcare, and PII. Attackers may steal or modify such weakly protected data to conduct credit card fraud, identity theft, or other crimes. Sensitive data may be compromised without extra protection, such as encryption at rest or in transit, and requires special precautions when exchanged with the browser.
Top 10 Web Application Security Risks according to OWASP are :
• A1:2017-Injection
• A2:2017-Broken Authentication
• A3:2017-Sensitive Data Exposure
• A4:2017-XML External Entities (XXE)
• A5:2017-Broken Access Control
• A6:2017-Security Misconfiguration
• A7:2017-Cross-Site Scripting XSS
• A8:2017-Insecure Deserialization
• A9:2017-Using Components with Known Vulnerabilities
• A10:2017-Insufficient Logging & Monitoring
The OWASP Top Ten Proactive Controls describes the most important control and control categories that every architect and developer should absolutely, 100% include in every project:
• C1: Define Security Requirements
• C2: Leverage Security Frameworks and Libraries
• C3: Secure Database Access
• C4: Encode and Escape Data
• C5: Validate All Inputs
• C6: Implement Digital Identity
• C7: Enforce Access Controls
• C8: Protect Data Everywhere
• C9: Implement Security Logging and Monitoring
• C10: Handle All Errors and Exceptions
Conclusion
Cyber hygiene must start as a board-level conversation. A top-down approach to create strong ransomware mitigation must establish a zero-trust access (ZTA). Make sure that your data is private and protected in transit, in use, in memory, and at rest. Sensitive data can be secured and protected by a robust data backup plan so systems can quickly be restored. A multi-layered defense can help to create a good security posture and how to discover unusual activity on your sensitive data. The advice from NIST, (ISC)2, OWASP, and ISO provides great starting points.







 News
News