How to Protect against Ransomware and other Attacks on Your Data
June 2021 by Ulf Mattsson, Chief Security Strategist at Protegrity
Basic cyber security hygiene should be implemented
You never know how the next attack on your data will enter your systems and the attacker may already be in your environment. Attackers constantly find new ways to avoid detection.
Make sure that your sensitive data stores are encrypted and implement a robust data backup plan. Test your restore procedures to make sure that your critical data and systems can quickly be restored from disconnected offline backup copies. A disaster recovery plan in addition to strong, multi-layer defense can help to create a good security posture.
Discover your sensitive data as a starting point
How do you discover sensitive data when many or most things can be sensitive? You first classify data, allowing users to categorize the type of data that can mostly be in the public domain. With those classifications established, the solution then leverages machine learning algorithms to discover that type of data. Classification and discovery find the data that needs to be protected.
A central enterprise policy
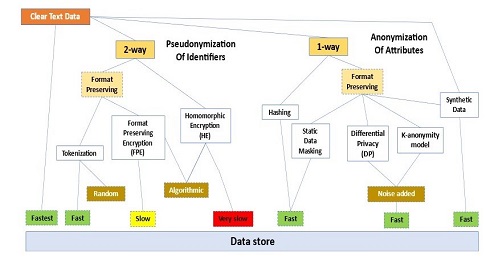
A central enterprise policy can control encryption keys and what data protection techniques that are used for different types of data:
You may also apply analytics and machine learning to discover unusual activity on your sensitive data.
Protect sensitive data
Make sure that your data is private and protected from manipulation by applying fine-grained data encryption or tokenization to limit exfiltration by ransomware and protect from other attacks on your data. This will protect data in transit, in use, in memory, and at rest. These are a general characteristics of fine-grained data protection, including encryption and tokenization
Examples of basic performance of fine-grained data protection, including encryption and tokenization:
Randomized data tokens can also protect against quantum computer attacks against encryption algorithms. These are a general scalability aspect of different approaches to data tokenization:
Examples of performance and scalability aspects of fine-grained data protection, including different encryption and tokenization approaches:
Course-grained encryption
For some types of data, you may consider using file level data encryption* to limit exfiltration by ransomware attacks and other attacks on stored data. This type of course-grained encryption will protect data at rest and files in transit:
*: Use safe algorithms and key-lengths that are resilient to quantum computer attacks against encryption algorithms and recommended by US NIST (National Institute of Standards and Technology).







 News
News