The realities of ransomware: Extortion goes social in 2020
September 2020 by John Shier, senior security advisor at Sophos
John Shier, senior security advisor at Sophos explains the growing threat of ransomware that threatens to publish companies’ private data.
The early days of ransomware were very much transactional. You received an unsolicited email, clicked on a link or opened an attachment, and your computer eventually ran the ransomware binary which encrypted all of your user-generated files. The process of recovery was fairly straightforward. You either recovered your files from backup (after doing a full re-image) or you sent Bitcoins to the criminals in exchange for the decryption key.
In time, the criminals added the ability to communicate with them and things got a little more personal.
These communications were mostly under the auspices of support. Not only could the criminals increase their reputation as ‘trustworthy’ merchants, but it also gave some individuals the ability to negotiate payment terms. In October 2019, the ransomware scene gave us a glimpse of things to come.
A group calling themselves ‘Shadow Kill Hackers’ attacked the city of Johannesburg, claiming to have stolen data from the city’s compromised systems. The difference here is that the attackers didn’t encrypt any files. In this purely social attack, the criminals threatened to release financial and personal data of Johannesburg’s citizens if payment (4 BTC) was not made by the deadline. The city rebuffed the ransom demand and the attackers were silent. It took less than one month for this new tactic to catch the attention of more serious ransomware gangs.
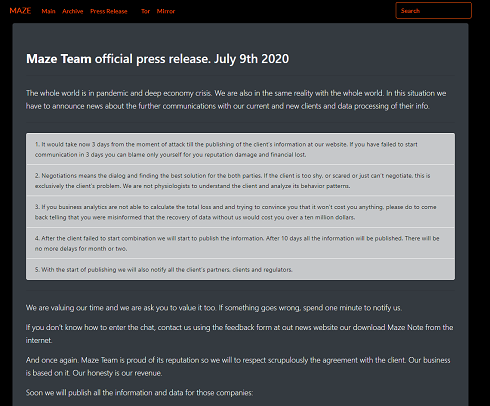
The Maze ransomware threat actors post regular updates to their website
The criminals behind Maze ransomware began incorporating this tactic of steal and share as additional extortion pressure in their ransomware operations. The first such incident occurred in November 2019 when the Maze crew released a portion of a victims’ stolen data in a show of force and added social pressure for the company’s lack of payment. Since then we’ve seen the Maze operators continue this behaviour and other prominent ransomware gangs have joined them.
Today it isn’t uncommon to hear of a ransomware victim being extorted into paying a ransom under threat of data exposure. We’ve seen some criminals use their total access to an organization’s compromised systems to pit employees against their own executives and IT department by threatening to release stolen employee data if the company did not engage with the criminals and negotiate payment.
While it’s still too early to determine if this form of social pressure will be more profitable than more traditional methods, it has heralded a new era in ransomware where social pressure and shaming is being used to increase the attackers’ bottom line.







 News
News