New technologies for data protection that arm innovative businesses to win
June 2021 by Ulf Mattsson, Chief Security Strategist at Protegrity
New technologies for data protection can arm innovative businesses to win in an ever-changing, increasingly competitive digital economy. Responsible businesses believe their customers and employees have a right to privacy—they value those relationships, after all. Unfortunately, success in safeguarding privacy, now and in the future, will not be guaranteed by a desire to do so. The myriad of regulations already enacted, compounded by the many others that are sure to come, only stress the need for businesses to protect the privacy of anyone and everyone whose personally identifiable information resides in corporate data.
New techniques for data protection create opportunities
New techniques for data protection create opportunities to harness the sensitive data that is proven to be most effective in activating advanced analytics, machine learning, and AI. Secure AI & Machine Learning (ML) Use-cases can include Analysis, Insight, Dashboarding, Reporting, Predictions, Forecasts, Simulation, and Optimization. Implementation of these approaches can lead to significant Savings and added Revenue:
Anonymization can minimize the risk of identification and Examples in Banking Credit Card Approval shows examples of Reducing the risk from 26% down to 8% while still maintain 98% accuracy compared to the ML Initial Model.
Privacy-preserving techniques for AI
Privacy-preserving techniques for AI – such as differential privacy or k-anonymity can ensure privacy of an individual’s sensitive data while also reducing bias in AI algorithms. We will review International Privacy Standards including reversable methods and non-reversable one-methods and discuss how Differential privacy gives a formal guarantee that individual-level information about participants in the database is not leaked.
Data must move without hindrance
Data must move without hindrance through an enterprise’s many cloud-based databases and applications. Businesses need the cloud to place workloads in development containers. They need the cloud to tap AI and reinvent how they make decisions. The types of data that are most critical in driving innovation—with advanced analytics, machine learning, and AI—are those deemed most sensitive and must be safeguarded. A common concern with cloud hosting is the risk of vendor lock-in, and an inability to migrate to another cloud service provider when features or pricing changes. Firms often adopt a “best of breed” cloud approach and end up with several providers. Some customers understand the liabilities implied by a “shared security model” or simply do not trust their hosting vendors to have full control of critical components like security of data, user accounts and applications.
Control of data security policies
So most firms want to have full control of data security policies and encryption keys and are quite familiar with their on-premises encryption and key management systems, so they often prefer to leverage the same tool and skills across multiple clouds. A centralized data security policy and encryption key management can leverage the same tool and skills across multiple clouds and for on-premises systems:
Data Security Management for Hybrid Cloud
Consistency, Trust and Vendor Lock-in and Migration
Most firms are quite familiar with their on-premises encryption and key management systems, so they often prefer to leverage the same tool and skills across multiple clouds. Firms often adopt a “best of breed” cloud approach. Some customers simply do not trust their vendors. A common concern is vendor lock-in, and an inability to migrate to another cloud service provider.
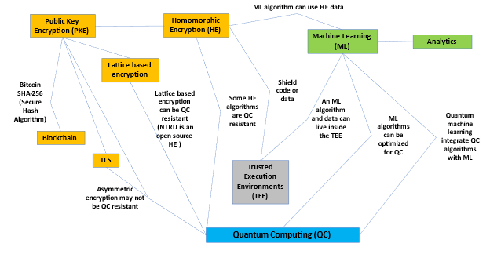
Machine Learning and Trusted Execution Environments
With machine learning models and data in Trusted Execution Environments (TEE) and the confidence that sensitive data is protected, businesses can quickly extract value, apply insights in real time, and predict outcomes that accelerate growth and “You don’t want me to know what stocks you’re trading, and I don’t want you to know the algorithm.” Operating on clear text information inside a TEE can also increase the speed compared to operating on homomorphically encryption data and provide scalability that is close to what you expect in cloud environment. You can shield machine learning models and data in TEE:
Homomorphic Encryption
Homomorphic Encryption, which allows computations on encrypted data and Machine Learning are growing in popularity. New Homomorphic Encryption algorithms that are secure from Quantum Computer-Based Attacks and machine-learning algorithm can be optimized for Quantum Computers.
While traditional encryption schemes can be used to privately outsource data storage to the cloud, the data cannot be used for computations without first decrypting it. This results in a huge loss of utility. For example, a secure cloud service may require a user to download their encrypted data, decrypt it locally, and perform necessary computations, instead of simply returning an encrypted result to the user.
Homomorphic encryption solves this problem, as it allows the cloud service to perform the computations while protecting the customer’s data with a state-of-the-art cryptographic security guarantee. The cloud only ever sees encrypted data, and only the customer can reveal the result of the computation. One of the advantages of the lattice-based cryptosystems mentioned earlier is that they can build systems that securely and privately handle computation on encrypted data.
The term homomorphic encryption may seem esoteric, but it just means encryption which you can compute on. Standard cryptosystems in use today don’t have this property: if you try to add together two ciphertexts (encrypted texts) encrypted using the Advanced Encryption Standard (AES), then the result will be gibberish. Homomorphic encryption differentiates itself by preserving the structure of the data. It encodes data in a mathematical object, and then encrypts it in a way that doesn’t affect the contained information. Homomorphic encryption is important because it allows consumers and enterprises to store their sensitive data in the cloud in encrypted form.







 News
News