Find and eliminate: more than a quarter of companies using EDR detect cyber-incidents in hours or less
July 2020 by Kaspersky
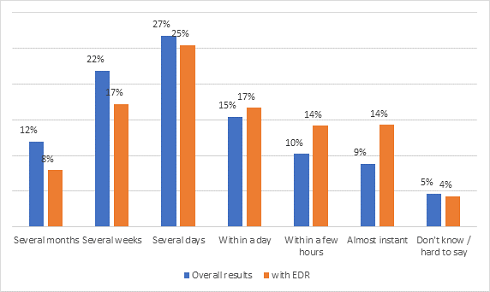
More than a quarter (28%) of companies that have implemented an Endpoint Detection and Response (EDR) solution have been able to detect cyberattacks in just a few hours or even almost immediately after an incident happened. This is higher than the overall results, as on average only 19% of businesses responded that way. This is the findings of the Kaspersky IT Security Risks Survey.
Timely detection of a cyber-incident is essential to reduce losses from a cyberattack. The longer that cybercriminals can stay unnoticed in a corporate network, the more data they can gather and the closer they can get to critical company assets. Reducing ‘dwell time’ allows businesses to contain a cyberattack before it can cause substantial damage.
In a survey of IT business decision makers commissioned by Kaspersky in 2019, 2,961companies around the world were asked how long it took them to discover a cyberattack that they experienced in the previous year. Detailed analysis of the given responses has revealed that there is a strong correlation between EDR implementation and dwell time.
Among the companies that use EDR, 28% confirmed that it took them several hours or less to find an attack. Of this group, 14% detected an attack almost immediately, which is higher than the average result of 9%. Meanwhile, 14% discovered the incident within a few hours, in comparison to 10% of overall respondents. Only 8% of EDR users said that it took them several months to identify that they were under attack.
However, the largest number of respondents estimated that detection took them several days, whether they have EDR in place or not.
Figure 1 - How long did it take to detect cyberattacks/incidents?
“EDR provides a greater level of discovery and visibility across endpoint infrastructure and facilitates effective root cause analysis, threat hunting and fast incident response. At the same time, EDR automates the routine tasks analysts may face in detection and response-processing activities. However, as the statistics show, for some respondents EDR doesn’t help to reduce an attack ’dwell time’. The reason may lie in the fact that alerts on suspicious activity require security analysts to investigate and decide if an action poses danger. So, in companies without internal expertise to handle complex incidents, the use of a feature-rich professional solution may not bring the desired effect,” comments Yana Shevchenko, Senior Product Marketing Manager at Kaspersky.
Kaspersky offers two EDR-class solutions that meet the requirements of different types of customers. For IT-security matured enterprises, Kaspersky EDR provides IT security experts with advanced threat discovery, deep investigative capabilities powered by threat intelligence and MITRE ATT&CK framework mapping, threat hunting and a centralised response to multi-staged complex attacks. Kaspersky EDR Optimum provides core EDR capabilities – including better visibility into endpoints, simplified root cause analysis and automated response options – to organisations with limited resources and cybersecurity expertise.







 News
News