New Variants of Agent.BTZ/ComRAT Found: The Threat That Hit The Pentagon In 2008 Still Evolving
August 2017 by Intezer
Agent.BTZ–also known as ComRAT–is one of the world’s oldest known state-sponsored threats, mainly known for the 2008 Pentagon breach. Technically speaking, Agent.BTZ is a sophisticated user-mode RAT developed and operated by the Turla group in conjunction with Snake/Uroburos rootkit. In the past few months, we conducted research on Agent.BTZ’s code-base and how it evolved using Intezer Code Intelligence™ technology. Based on our research conclusions, we were able to hunt about a dozen new samples and more than seventy previously unknown live IP & DNS addresses indicating the ongoing abuse of satellite internet providers operating in both Africa & the Middle East.
This is a short memo regarding our findings from the past few months; in a few days, we will publish a whitepaper (part 2/2) describing in more details how we found these new variants using our technology, along with a thorough analysis of the new samples.
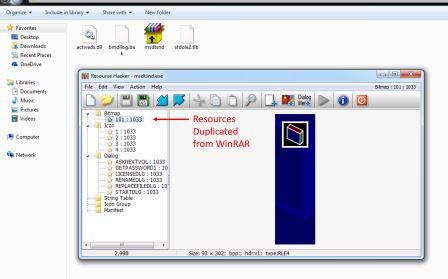
Dropper: Although the code itself was written from scratch and has nothing to do with WinRAR, the adversary tried to mimic WinRAR’s SFX installer. Resource data was duplicated, including icons and layouts used by the original installer, as you can see in the following screenshot:
Once executed, the dropper installs activeds.dll – a proxy dll which is loaded directly to explorer.exe once the machine reboots. The purpose of this proxy dll is to load the malware’s main payload –
stdole2.tlb. The dropper then also deletes any previous installation of Agent.BTZ if it exists. This is done using a hard-coded file path:
“C:\Documents and Settings
“C:\Documents and Settings
**Note: These file names were first used by Agent.BTZ in late 2014, as you can see in this automatic Dr.WEB report
Once finished, the dropper renames and self delete using the following command line:
“C:\WINDOWS\system32\rundll32.exe C:\DOCUME 1
Samples found:
1 69690f609140db503463daf6a3699f1bf3e2a5a6049cefe7e6437f762040e548
2 6798b3278ae926b0145ee342ee9840d0b2e6ba11ff995c2bc84d3c6eb3e55ff4
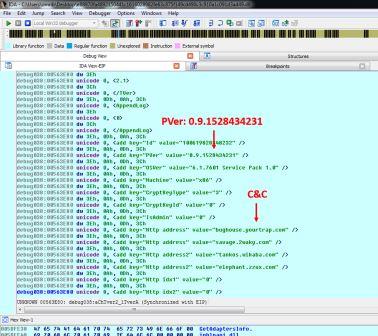
stdole2.tlb: As previously mentioned, this file is the main component installed by the fake-sfx dropper and loaded by activeds.dll. We extracted the configuration from each sample in order to obtain the c2 address and inner version (“PVer”), which is built into every Agent.BTZ sample. In the past, Agent.BTZ’s developers have used an incremental value to indicate the inner build version, the last known value is 3.26 as published by G-Data in late 2014, It seems that the developers have reacted to G-Data’s publication and have stopped using an incremental value. New variants are now using a different numbering system of 0.8/9.
**example configuration extracted from one of the samples – PVer 0.9.1528434231.
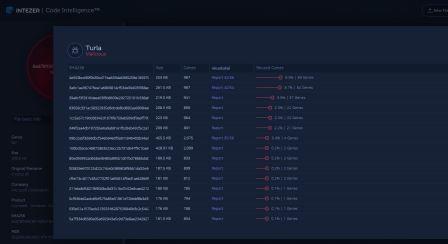
Even without the PVer numbering, we were able to determine using our technology that these samples are from a newer version, which is based on the latest known versions of Agent.BTZ – 3.25 / 3.26. These are the two top files you can see in the following screenshot:
4e553bce90f0b39cd71ba633da5990259e185979c2859ec2e04dd8efcdafe356(VirusTotal)
3a6c1aa367476ea1a6809814cf534e094035f88ac5fb759398b783f3929a0db2(VirusTotal)
Both of these files were uploaded almost three years ago to VT(!)
**A screenshot from the Intezer Code Intelligence™ product displaying a list of files in our database that share pieces of code with one of the new samples. These pieces of code are specific to the Turla malware family, and were not seen in any other malicious or legitimate software.
Related articles:
https://www.gdatasoftware.com/blog/2014/11/23937-the-uroburos-case-new-sophisticated-rat-identified
https://www.gdatasoftware.com/blog/2015/01/23927-evolution-of-sophisticated-spyware-from-agent-btz-to-comrat
http://blog.threatexpert.com/2008/11/agentbtz-threat-that-hit-pentagon.html
https://securelist.com/satellite-turla-apt-command-and-control-in-the-sky/72081/
https://www.symantec.com/content/en/us/enterprise/media/security_response/whitepapers/waterbug-attack-group.pdf
https://securelist.com/the-epic-turla-operation/65545/
http://artemonsecurity.com/snake_whitepaper.pdf
https://www.gdatasoftware.com/blog/2015/01/23926-analysis-of-project-cobra







 News
News